This site uses cookies to provide you with a more responsive and personalized service. By using this site you agree to our use of cookies. You can learn more about our use of cookies and similar technologies and your choices by reviewing our Privacy Policy. By clicking “I agree” you agree to our use of cookies and similar technologies.
Corporate Internal Investigations
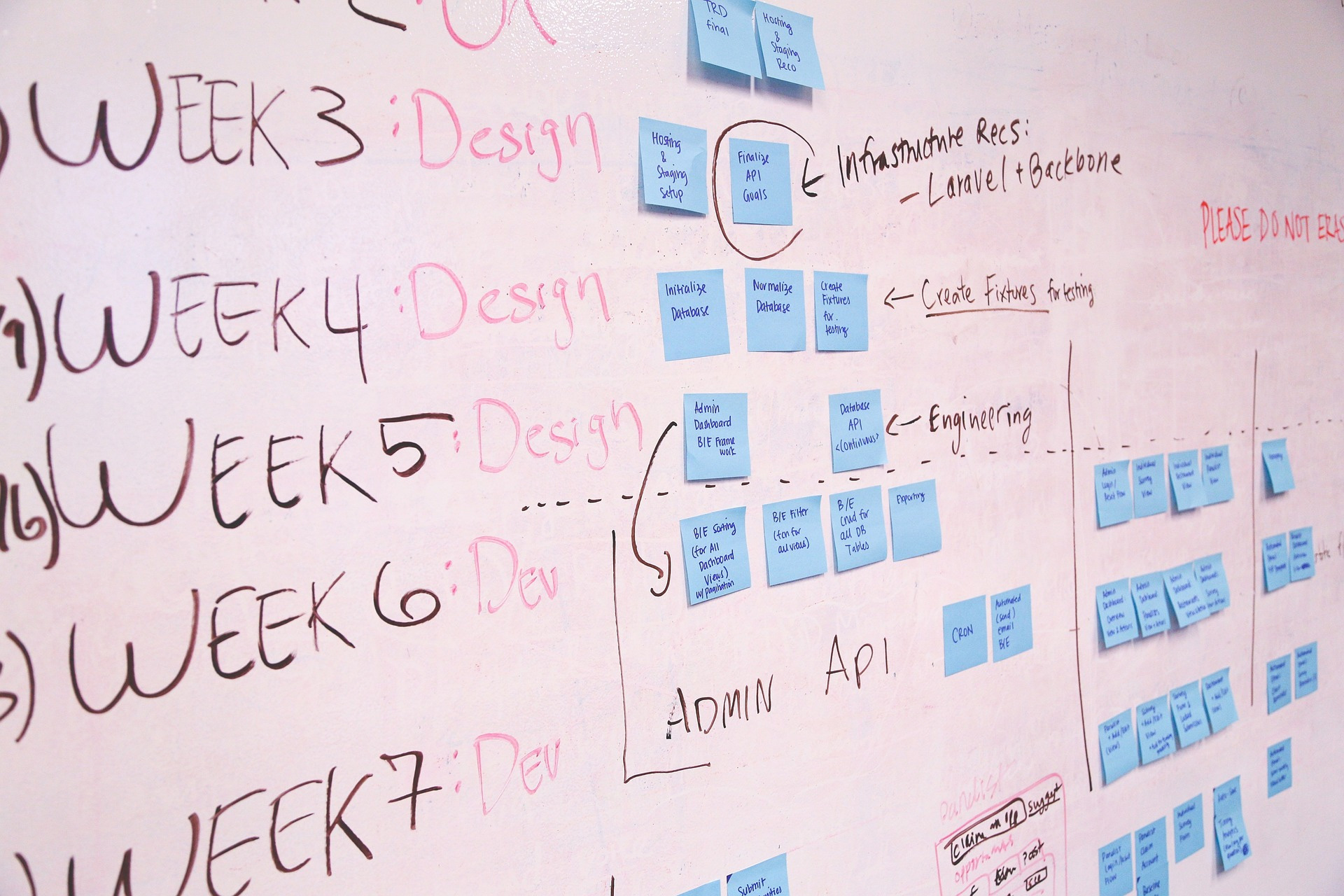
We are frequently called upon to conduct internal investigations into allegations or suspicions of harassment or corrupt or fraudulent conduct by employees. We rely upon our team of attorneys, forensic accountants, research analysts, field investigators and computer forensics experts to staff these assignments, and we work collaboratively to develop an investigative plan that is appropriate to the suspected misconduct.
We typically employ a phased approach to internal investigations, with budgetary parameters for each phase. The scope and focus of successive phases are determined in consultation with you, and our strategy going forward is dictated by the findings in each phase. Since most of our investigative professionals have had experience in federal, state and local law enforcement — as prosecutors, auditors and agents — our strategies are developed with an understanding of the evidence that may be needed to support an eventual criminal prosecution.
Because we have years of experience in the private sector, we are equally sensitive to matters of confidentiality and public perception. When an investigation becomes public, it is critical that every effort is made to protect your organization from reputational damage. With input from strategic partners with experience in such matters, we often assist in developing an appropriate public response to inquiries regarding the suspected misconduct.
Asset Searches + Recovery
Monetary trails invariably remain when an unsuspecting employer or trusting investor is defrauded. Identifying and following these trails is the foundation of most financial investigations. We excel in finding and recovering assets on behalf of trustees, creditors’ committees, corporations and individuals, both domestically and globally, to uncover hidden assets, wherever they may be secreted.
We have a track record of success with asset searches and recovery in numerous jurisdictions. We have worked extensively in jurisdictions which provide offshore asset secrecy and protection, e.g., the British Virgin Islands, Bermuda, the Bahamas, the Caymans, Channel Islands, the Seychelles, Mauritius, Switzerland, Liechtenstein, Luxembourg, Monaco, Cyprus, Panama and other countries in Central America, and various countries in Asia. Our success also includes investigations and recoveries in South America, the United States, Canada, the United Kingdom, India, Pakistan, Egypt, the United Arab Emirates, the former Soviet states, Scandinavia, and a number of other Middle Eastern and African nations.
Asset searches begin with background investigations on any related parties in order to identify evidence of assets held by these individuals. Expert investigators search public and proprietary databases and conduct discreet interviews of relevant witnesses where necessary. Research on corporate entities involved in the matter is conducted to develop general profiles of such companies and identify assets held by them.
Research is performed using a variety of public record resources, including:
- Corporate filings
- Real property records
- Motor vehicle, watercraft and aircraft ownership
- Federal and state criminal proceedings
- Federal and state civil litigation
- Bankruptcy proceedings
- Lien and judgment filings
- Uniform Commercial Code (UCC) filings
- Reviews of media sources and Internet websites
Our team has conducted more than 100 financial investigations involving embezzlement, fictitious billing scams, inventory theft, and high-profile bankruptcy fraud matters. The team includes forensic accountants and investigators who have mastered the skill of making the distinction between irrelevant and crucial data, and extracting the evidence necessary for success. The investigator must not only see what is there, but also what should be and is not.
Big Data Investigations
We can successfully assemble, standardize and integrate massive amounts of transaction level data from different sources to identify patterns and linkages potentially indicative of suspect activities that would be hidden or difficult to detect with traditional methods.
We offer the following effective tools in matters involving into Big Data:
Guidepost Insight™
This data-as-a-service platform that enables vast amounts of data to be gathered, indexed, displayed and correlated. Its ability to collect and aggregate vast amounts of data significantly impacts the speed, efficiency and cost-effective manner in which investigations can be carried out. Guidepost Insight connects data across multiple sources, automatically creates relationships and visualizes findings in real time. It does this by capturing every bit of data or text relating to a topic or case, supplemented by data available from external data sources. Results can be output in any way you like to quickly highlight relationships, patterns, trends and anomalies.
Siron® Anti-Financial Crime Products
The building-block design allows variable combination of the products to fulfill custom requirements for governance, risk and compliance in the best possible way. The products consistently follow the risk-based approach and support all phases of the compliance process with integrated solution modules: from specific risk analysis and continual risk classification to monitoring of transactions and behavioral patterns, and central case management with risk and compliance dashboards. Siron® products are highly standardized and parametrizable. They can be combined at will to create custom solutions. Numerous best-practice scenarios from a large number of customer installations have made their way into these standard research products. They guarantee fast roll-out of professional solutions based on the latest compliance knowledge. The technology is robust, interoperable, platform-independent and highly scalable. This facilitates integration of Siron® products into existing system environments and provides seamless interaction with third-party applications and databases. The field of application extends from the lean departmental to a cross-organizational and multinational group solution.
Siron® anti-financial crime products consist of flexible software modules for:
- Anti-money laundering
- Counter-terrorism financing
- Know your customer
- Tax compliance & reporting (e.g. FATCA, CRS)
- Risk assessment & risk controlling
- Business partner due diligence
- Giant Oak Search Technology (GOST™)
Guidepost Solutions LLC offers Giant Oak Search Technology (GOST™), a fast, reliable negative media search tool. As an analyst or investigator working for a financial institution, you need to perform negative media searches on a tremendous amount of customers. By leveraging domain specific indexes of the internet, GOST™ uses a sophisticated risk-scoring method that targets the right kind of information on countless customers, so you can focus on where to begin. It then provides a dossier on each individual with everything you need to know, such as web page images, and keywords already highlighted to help you identify who you want to work with and who you don’t. Should any negative information surface later, GOST™ provides an audit trail that can be used to defend the decisions you made. With GOST™, you can efficiently focus your searches in a matter of minutes.
Cybersecurity Investigations
We regularly advise attorneys and corporate clients on preserving, analyzing and utilizing computer evidence in litigation, regulatory proceedings, presentations to law enforcement and governmental investigations. We perform all forensic investigations under the assumption that court testimony will be required and adhere to law enforcement standards of chain of custody and evidence storage.
We understand that computer forensics may be used for a variety of tasks, such as finding the “smoking gun” email, proving deliberate spoliation by an opposing party, or trying to make sense of suspicious computer activity on the day a key employee departed. We specialize in focused, aggressive computer investigations into intrusions, internal misconduct, phishing scams, malicious software and other digital attacks. Our unique capabilities, relationships and tools, coupled with professionals who convert “tech-speak” into valuable information, enhance both responsiveness and investigative efficiency – nationwide and on a moment’s notice.
Our professionals are expert in the forensic analysis of data from all Windows, Mac and Linux computers and servers; mobile devices; and Cloud-based platforms and applications. Our investigators have experience as court-appointed experts and in giving testimony under cross-examination, regularly testify as experts in state and federal courts, liaise with law enforcement and regulators, and work with investigative professionals to provide a seamless investigation.
Intellectual Property
Intellectual property is often among a company’s most valuable assets and too frequently an enticing target for those who counterfeit, divert, exploit or otherwise misappropriate such assets. This is true whether the target involves counterfeit or diverted software, films, music, pharmaceuticals, luxury goods, consumer brands or industrial intellectual property assets.
We have the knowledge and experience to help harden intellectual property targets and effectively respond to the individuals and organizations that perpetrate intellectual property crime.
Our IP protection programs employ the optimal physical security, cybersecurity, marking technologies, intelligence collection efforts and procedures and protocols to help you avoid, detect and respond to attacks. These programs are deployed both at client facilities and at multiple points of the supply and distribution chains to effectively prevent the unlawful creation and dissemination of unauthorized product and to quickly identify and recover unauthorized product in the marketplace.
Our investigators and intelligence operatives are expert at developing information on unauthorized manufacturers and distributors of illegally produced products. Our team has experience working with law enforcement officials and other parties throughout the world to shut down, disrupt or deter the misappropriation of intellectual property.